Computer Forensics techniques. Steganography. Network Surveillance. Protection and Monitoring of National Infrastructure assets.
HI119V IT-Security II: Computer Forensics 7.5 credits
This course has been discontinued.
Decision to discontinue this course:
No information inserted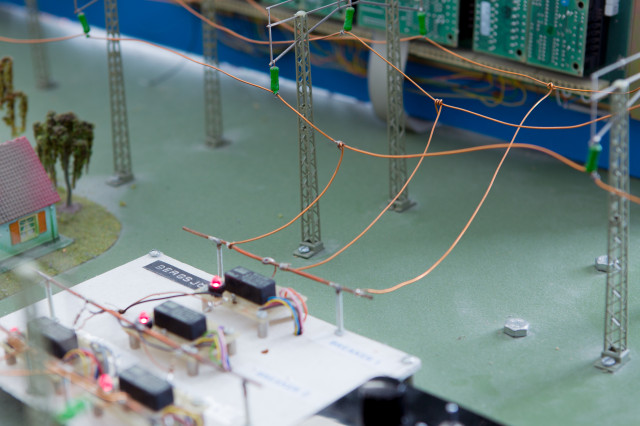
Information per course offering
Course offerings are missing for current or upcoming semesters.
Course syllabus as PDF
Please note: all information from the Course syllabus is available on this page in an accessible format.
Course syllabus HI119V (Spring 2012–)Content and learning outcomes
Course contents
Intended learning outcomes
After the project course the student should know:
- The principles of Computer Forensics
Literature and preparations
Specific prerequisites
Completed upper secondary education including documented proficiency in English corresponding to English A.
Recommended prerequisites
Knowledge corresponding to the course HI117V IT-Security I (formerly 6H4081)- for furher information in English, please contact the teacher.
Literature
Handbook of Computer Crime Investigation;
Forensic Tools & Technology,
Eoghan Casey, 2001, 448 pp
Academic Press,
ISBN-10: 0121631036
ISBN-13: 9780121631031
Digital Evidence and Computer Crime, 2nd edition,
Eoghan Casey, 2004, 688 pp
Academic Press,
ISBN-10: 0121631044
ISBN-13: 9780121631048
Digital Course Notes
IT-Sec II, 3 CDs, 1.5 GB,
L.O. Stromberg
Examination and completion
Grading scale
Examination
- TEN1 - Examination, 3.0 credits, grading scale: A, B, C, D, E, FX, F
- ANN3 - Assignment, 1.5 credits, grading scale: P, F
- ANN1 - Assignment, 1.5 credits, grading scale: P, F
- ANN2 - Assignment, 1.5 credits, grading scale: P, F
Based on recommendation from KTH’s coordinator for disabilities, the examiner will decide how to adapt an examination for students with documented disability.
The examiner may apply another examination format when re-examining individual students.
If the course is discontinued, students may request to be examined during the following two academic years.
Examinations are offered three times a year: typically the first Saturday in May, August, and December.
Written examinations are four hours long, and consist of 68 questions; 60 of which are multiple choice (5 choices each) and 8 are in depth questions, including mathematical calculations. The Final examination in IT-Sec III is a lab project.
Written examinations worldwide can usually be arranged at other universities, as well as at Swedish embassies and consulates.
Examiner
Ethical approach
- All members of a group are responsible for the group's work.
- In any assessment, every student shall honestly disclose any help received and sources used.
- In an oral assessment, every student shall be able to present and answer questions about the entire assignment and solution.
Further information
Course room in Canvas
Offered by
Main field of study
Education cycle
Supplementary information
KTH was the first university in Northern Europe to establish academic computer forensics courses, in cooperation with national and international forensics agencies. Our courses are intended for working professionals, as well as for senior undergraduate, graduate and postgraduate students.
For Whom:
is a KTH graduate, who has worked professionally for 3-5 years, and now wants to come back to specialize in his/her field. Many of our professionals typically study one whole day each weekend and 2-3 evenings per week. Average study time in each course is typ. 15-22 hrs/week, depending on background and experience.
Course availability:
Our courses can be taken from anywhere in the World, as distant education courses. Over the years our students have been located in North and South America, Europe, Asia, Africa and Australia. In most cases you can even take the final exam in a foreign country.
Course Material:
All of our course material is in English. In addition to the course textbook(s), we also make available about 1.5 Gigabyte of additional course material, including lectures, course notes, course assignments and reference material in each course, on three CDs (updated annually).
Whole day seminars / lectures / workshops:
In each course, we also offer four whole day (7h) Saturday seminars / lectures at KTH in Stockholm during each semester. Attendance is voluntary, but highly recommended. Recordings are made available to students with learning disabilities.
SSS:
A custom-designed student support system (SSS) enables our students keep their contact info updated, obtain course information, submit course assignments and course papers – and receive immediate receipt in writing on all submissions 24/7 from anywhere in the World. SSS was specifically designed to work through most government and corporate firewalls.
Admission:
KTH Students should contact their Academic Advisor or program coordinator. External Students should apply through the national website for higher education:http://www.studera.nu